How to Implement the HIPAA Security Rule: Three Pillars
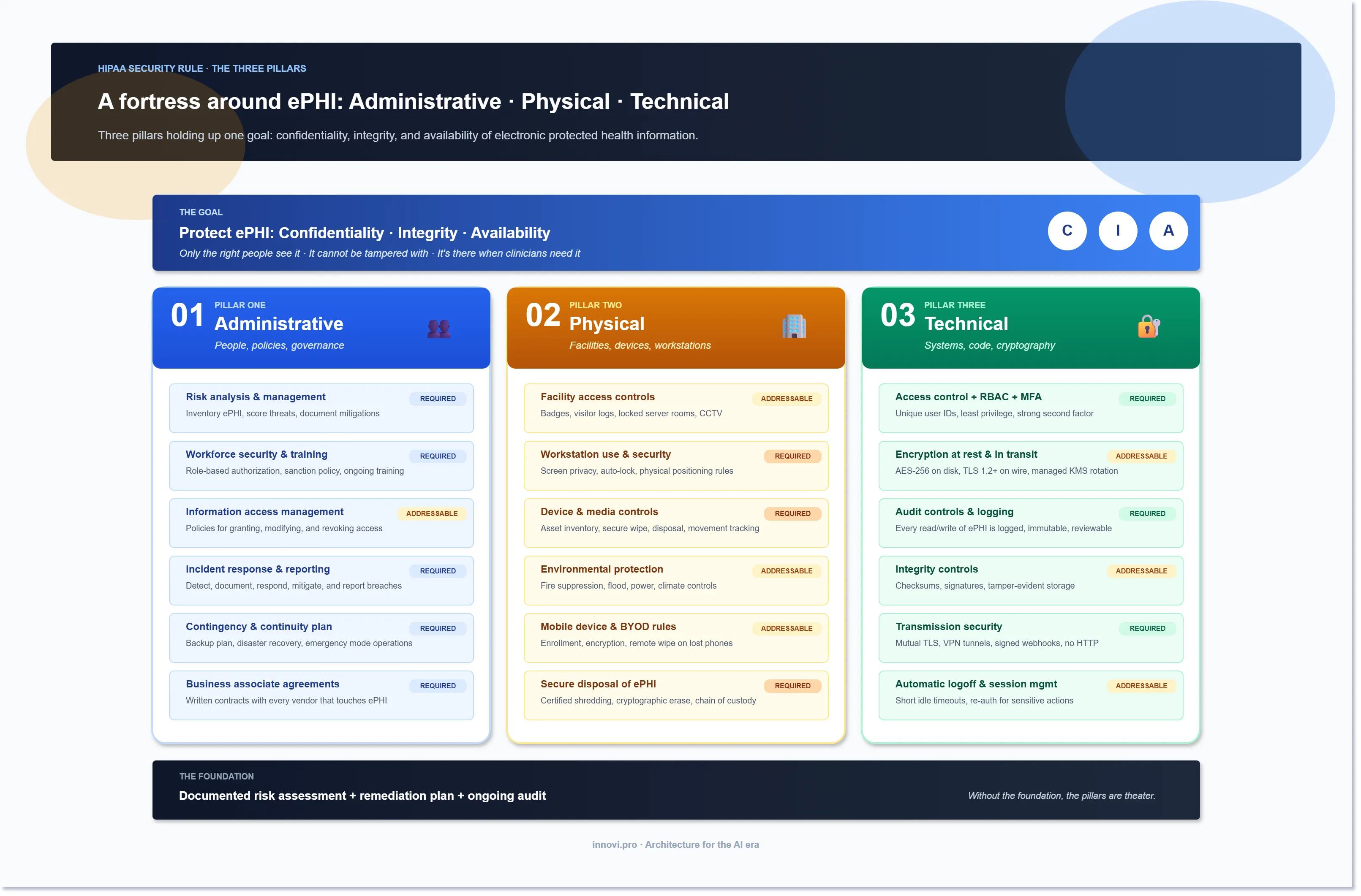
The HIPAA Security Rule is not a checklist. It is three pillars — administrative, physical, technical — standing on one foundation: a documented, current risk assessment. Skip the foundation and the rest is theater.
OCR can fine you up to $1.5 million per category per year, but the bigger cost is trust: a single breach headline erases a decade of patient goodwill. This guide walks each pillar with the specific controls to implement, which ones are Required, and which are Addressable.
What is the HIPAA Security Rule?
The HIPAA Security Rule is a federal law that establishes national standards to protect individuals' electronic personal health information (ePHI). The Security Rule requires appropriate administrative, physical and technical safeguards to ensure the confidentiality, integrity, and security of ePHI.
HIPAA Security Rule compliance is mandatory for all healthcare providers, health plans, and healthcare clearinghouses that electronically transmit health information. It also applies to their business associates, such as third-party administrators, billing companies, and cloud storage providers.
The penalties for HIPAA Security Rule noncompliance can be severe. The Office for Civil Rights (OCR) is responsible for enforcing HIPAA regulations and can impose fines of up to $1.5 million per year for violations. In addition to financial penalties, organizations may also face reputational damage and loss of patient trust.
Implementing the HIPAA Security Rule
The HIPAA Security Rule isn't just a set of checkboxes; it's a framework for building a comprehensive security program to protect your patients' most sensitive information. Think of it as constructing a fortress around your electronic protected health information (ePHI), with multiple layers of defense working together to prevent unauthorized access and data breaches. This section will guide you through the key steps in implementing the HIPAA Security Rule, laying the foundation for a secure and compliant healthcare environment.
Conduct Risk Assessment
A risk assessment is a thorough evaluation of potential threats and vulnerabilities to ePHI. It is a critical step in implementing the HIPAA Security Rule, as it helps you identify areas where your organization is at risk and take steps to mitigate those risks. This is not a one-size-fits-all exercise; it requires a deep dive into your specific environment, considering factors like the type of ePHI you handle, your technology infrastructure, and your workforce.
To conduct a risk assessment, you will need to:
- Identify where ePHI is stored, transmitted, and processed in your organization.
- Assess the likelihood and impact of potential threats to ePHI.
- Evaluate the effectiveness of your current safeguards.
Develop a Remediation Plan
Once you have completed your risk assessment, you need a battle plan to address the vulnerabilities you've uncovered. That's where the remediation plan comes in. It's a roadmap for strengthening your defenses and closing any security gaps. This plan should be prioritized, actionable, and regularly reviewed to ensure its effectiveness.
A remediation plan is a documented plan that outlines how you will address the risks identified in your risk assessment. The remediation plan should include:
- A prioritized list of risks
- Specific action steps to address each risk
- A timeline for completing each action step
- A plan for monitoring the effectiveness of your remediation efforts
How Innovi Pro Can Help with HIPAA Risk Assessment and Remediation
- We can help you conduct a comprehensive risk assessment.
- We can help you develop a remediation plan to address any identified risks.
- We can help you implement security measures to mitigate risks.
Create Policies and Procedures
Policies and procedures are essential for ensuring that your organization complies with the HIPAA Security Rule. Your policies and procedures should address all aspects of the Security Rule, including data security, access controls, and employee training. These documents should be clear, concise, and readily accessible to all members of your workforce.
How Innovi Pro Can Help with HIPAA Policies and Procedures
- We can help you develop and document HIPAA-compliant policies and procedures.
- We can help you ensure that your policies and procedures are regularly reviewed and updated.
Employee Training
Your employees are the gatekeepers of your patients' most sensitive information. Even with the strongest technical and physical safeguards in place, human error remains one of the biggest risks to ePHI security. A misplaced laptop, a weak password, or simply falling victim to a phishing scam – these are all too common scenarios that can lead to a data breach. That's why comprehensive HIPAA Security Rule training is not just a regulatory requirement, but a crucial investment in protecting your organization and your patients. It's about empowering your workforce to become active participants in your HIPAA compliance efforts.
All employees who have access to ePHI must receive HIPAA Security Rule training. Training should cover the following topics:
- An overview of the HIPAA Security Rule
- The importance of protecting ePHI
- The organization's policies and procedures for protecting ePHI
- The employee's role in protecting ePHI
At Innovi Pro, we understand the critical role that employee training plays in HIPAA compliance. All our employees undergo comprehensive HIPAA Security Rule training, ensuring that we are well-equipped to assist our clients in developing and implementing effective training programs.
Physical Safeguards
It's easy to get caught up in the digital world of firewalls and encryption when thinking about HIPAA compliance. But let's not forget the physical world where patient data lives – on computers in offices, on laptops carried by staff, and on servers tucked away in data centers.
Think of every workstation and device that can access ePHI as a potential entry point for a data breach. A laptop left unattended in a coffee shop, a smartphone stolen from a car, or even a desktop computer left logged in overnight – these are all vulnerabilities.
Physical safeguards are designed to protect ePHI from unauthorized access and environmental threats. Physical safeguards include:
- Securing workstations and devices
- Implementing access controls and surveillance
- Protecting against environmental threats such as fires and floods
Technical Safeguards
Technical safeguards are designed to protect ePHI through the use of technology. This goes beyond simple passwords and backups; it's a multi-layered approach to ensure your systems are truly HIPAA compliant.
Technical safeguards include:
- Strong passwords and multi-factor authentication
- Regular data backups
- Data encryption and access controls
- Monitoring and auditing tools
Let's take a closer look at some of the key technical safeguards required by the HIPAA Security Rule.
Access Control and User Authentication
It's not just about keeping the bad guys out; it's also about making sure the right people have the right level of access. Role-based access controls (RBAC) are a cornerstone of HIPAA compliance. Imagine a scenario where a receptionist could accidentally access a patient's entire medical history, or a billing clerk could modify a patient's diagnosis. RBAC prevents such scenarios by granting access based on job roles and responsibilities. Each user has a unique ID and is only allowed to access the information necessary for their specific tasks.
Encryption at Rest and in Transit
Encryption is the process of scrambling data into an unreadable format, making it virtually useless to anyone who doesn't have the decryption key. HIPAA mandates encryption for ePHI both "at rest" (when stored on your servers or devices) and "in transit" (when transmitted over networks). This ensures that even if a hacker manages to intercept the data, they won't be able to make sense of it.
Data Backups and Disaster Recovery
Accidents happen. Hard drives crash, ransomware attacks cripple systems, and natural disasters can wreak havoc on your IT infrastructure. Regular data backups are your safety net, ensuring that even if the worst happens, you can recover your ePHI and restore operations. HIPAA also requires that you have a disaster recovery plan in place, outlining the steps you'll take to get your systems back online and your data restored in the event of an emergency.
Monitoring and Auditing
It's not enough to simply put safeguards in place; you also need to keep a watchful eye on your systems. Monitoring and auditing tools track user activity, data access, and any suspicious behavior that could indicate a potential breach. These tools not only help you detect breaches but also provide valuable data for your incident response efforts.
How Innovi Pro Can Help with HIPAA Technical Safeguards
- Develop and deploy SSO (Single Sign-On) solutions to simplify access management and implement RBAC (Role-Based Access Control) to ensure that users have the appropriate level of access.
- Implement encryption protocols to secure ePHI both at rest and in transit.
- Set up automated data backup solutions and disaster recovery plans to ensure business continuity in the event of a data loss incident.
- Deploy monitoring and auditing tools to track user activity and detect potential security incidents.
Conclusion
Protecting your patient's sensitive health information is not just a legal requirement; it is a fundamental aspect of providing quality care. The HIPAA Security Rule can seem complex, but by breaking it down into smaller steps – risk assessment, remediation planning, policy creation, employee training, physical safeguards, and technical safeguards – you can build a robust security framework.
Implementing these measures demonstrates your commitment to patient privacy and data security. It helps you avoid potential fines and fosters trust among your patients. Remember, HIPAA compliance is an ongoing journey, not a one-time destination. As technology evolves and new threats emerge, you must adapt and strengthen your security posture continuously.
If you need assistance navigating the complexities of the HIPAA Security Rule, contact us for a consultation. Our team of experts can provide you with the guidance and support you need to protect your patient's data and ensure HIPAA compliance.
